Isn’t my data already backed up?
GitHub Terms of Service
You understand and agree that we will not be liable to you or any third party for any loss of profits, use, goodwill, or data, or for any incidental, indirect, special, consequential or exemplary damages, however arising, that result from…
Maybe – but can you restore it?
SaaS providers, including GitHub, operate using the Shared Responsibility Model.
GitHub maintains a disaster recovery plan for its entire platform – Rewind protects the individual account-level data you rely on.
So if a hurricane struck, GitHub could restore its entire platform.
But, if you suffered from a more common risk (e.g. cyberattacks, mistakes, or malicious deletion), your data could be gone forever.
Rewind backs up and restores account-level data. Item-level or full account restores ensure you can recover from any data disaster.
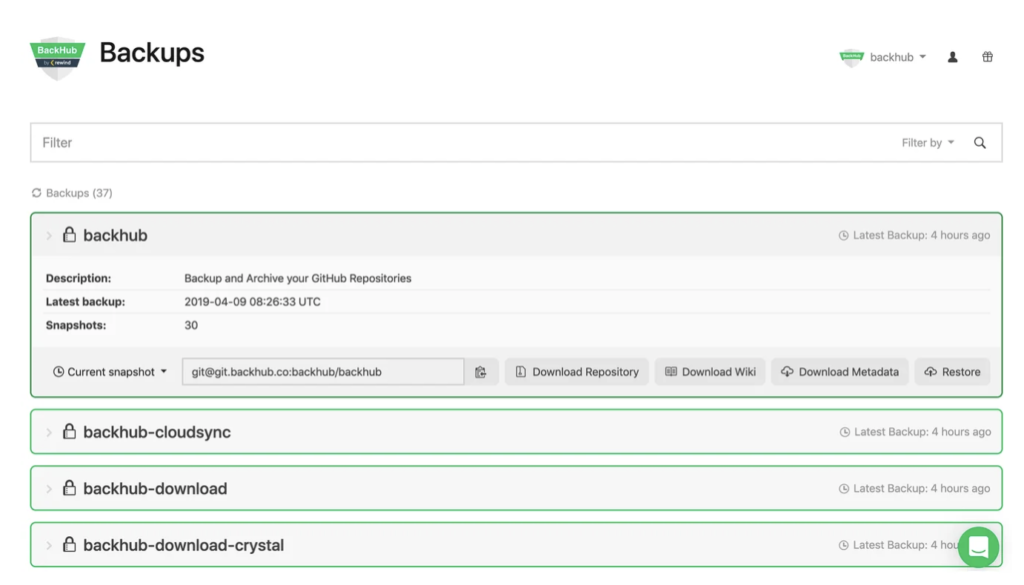
Key Features of Rewind for GitHub
Daily Backup Snapshots
Quickly restore a previous state of your repository with Rewind’s daily snapshots, including metadata, up to 365 days back in time.
Backup Issues, Milestones, and More
Backups include not only the repository with all branches, but also all associated metadata, such as issues, milestones, pull requests, releases, wikis and more.
Clone from Rewind Servers
Clone any snapshot of your GitHub backup directly from Rewind, giving you access to your code and repository data any time—even during a GitHub outage.
Automatic Cloud Sync
Keep an additional backup copy on your own storage as long as you need. Rewind supports Amazon S3 and Azure Storage.
Download Repositories and Metadata
You can download the GitHub repository or metadata directly from Rewind without having to restore it back to GitHub.
Audit Log for Enterprise Compliance
The audit log is a centralized stream of all system and user activity within your Rewind installation. Easily monitor your backups and account activity.
Creating your first GitHub backup with Rewind
- Start your 14-day free trial of Rewind on GitHub Marketplace.
- Choose which account to backup with Rewind.
- Grant Rewind read-only permission to your repositories and start generating comprehensive automatic backups.
Try Rewind free for 14 days
Note: Please visit our Enterprise page for Enterprise Plans.
Rewind is now proudly SOC 2, Type 2 compliant
Rewind is the leading third-party provider of SOC 2-compliant cloud backups. Our full SOC report and detailed security portal is available upon request.

CCPA
GDPR
PIPEDA
SOC 2
SOC 3
Learn more about Rewind
- Reviews & Testimonials
- Data & Security Portal
- Documentation
- Downtime Calculator
- Pricing Information
- Terms of Service